Name resolution makes life easier for everything so today I’ll show you how I’ve setup my pfSense device to perform DNS resolution on devices registered via pfSense DHCP.
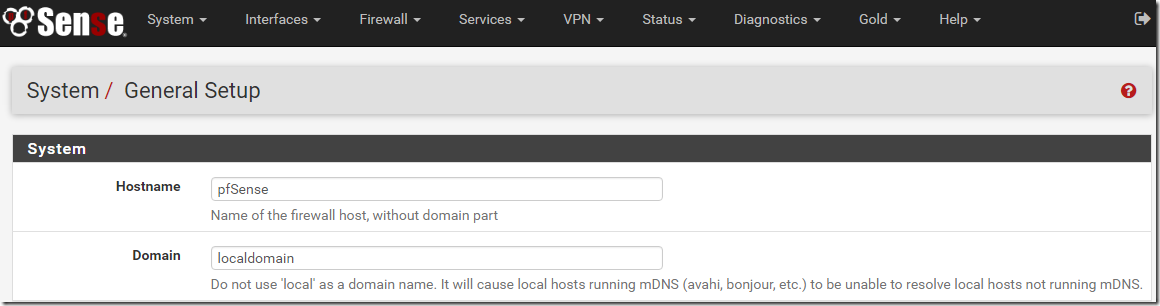
pfSense General Setup – Domain
In this example I’m going to use the default domain name configured with pfSense. Obviously this should be tweaked for your specific needs but if you are running this at home then localdomain is fine. My home lab actually has it’s own Active Directory DNS servers and I configure pfSense to forward any requests for that lab domain to those DNS servers.
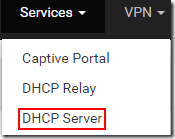
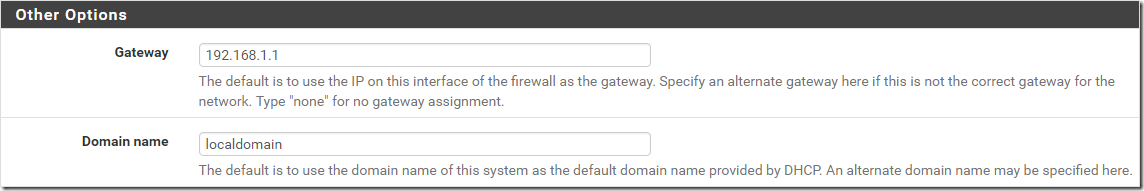
pfSense DHCP Server Domain Name Configuration
Having picked our domain name we need to check that the DHCP server in pfSense is configuring said name when issuing an address lease. Browsing to the ‘Services’ menu and then selecting ‘DHCP Server’ we need to scroll down to the ‘Other Options’ section. By default pfSense will use the name defined under the system setting we checked earlier. If you want to configure an alternate name for a specific DHCP range (e.g on a different subnet) you can do so here. If like me you prefer to see the option that is being used when scrolling through a config then add the domain here implicitly.
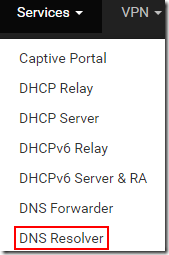
pfSense DNS Resolver Settings
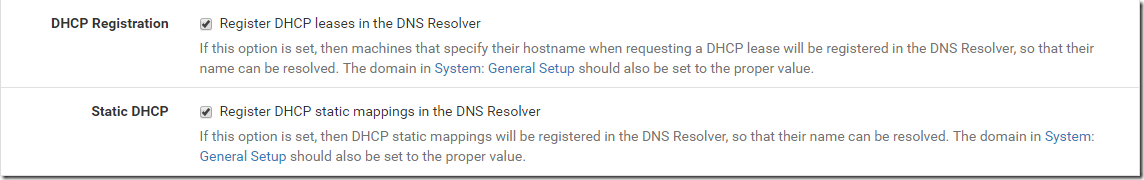
Now we can configure the pfSense DNS resolver settings to register DHCP leases in DNS to allow for easy name resolution. Browse to the ‘Services’ menu and select ‘DNS Resolver’.
Scroll down and select to register DHCP leases and if you are using static DHCP mappings, register those as well.
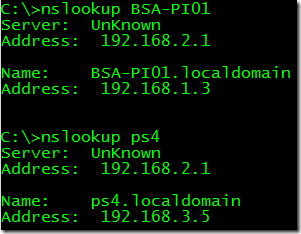
Testing Name Resolution
From my PC I now run a name resolution check to see if a Raspberry Pi I have configured on my network for dynamic DHCP has registered in DNS correctly and can be resolved. I also test to see if my Playstation 4 is resolved – it has a static registration so I’m showing that both dynamic and static entries are registering, just as we configured.
The pfSense DHCP and DNS settings provide you with a huge range of options, certainly more than I have shown in this post, hopefully if you are looking to do something similar this post will assist you.
This doesn’t work for me and I can’t seem to figure out why. Do your clients need any sort of configuration?
Hi Chuck,
Clients shouldn’t need any special configuration other than to receive DHCP information from pfSense. What happens when you test name resolution?
Alex
Oh… My… God… You saved my life… I was pulling my hair trying to figure this out. I Googled on several forums for people asking similar questions and many pfSense zealots were answering RTFM or answering in a patronizing way…
I believe pfSense is victim of its great versatility. Since you can configure and have it do just about anything, the common use cases are spread across several screens which have several fields with terms that are not evident for people unfamiliar with configuring firewall related stuff. I strongly believe that pfSense would benefit from at least having wizards to do the basic stuff, and at the end of the wizard, it could provide hyperlinks to all related screens if the user wants to fine tune all the plumbings that was done by the wizard. Some could argue that the screens are tailored for professionals working in business. I would argue that you’re a beginner before becoming a professional and thus such wizards could help people ramp up more quickly, thus pfSense could get wider adoption.
Anyway, thanks again!
So glad I could help, it is a challenge getting the information you need at times. That is what lead me to start blogging in the hope I can help others every now and then.
This works when using the CLI, but it doesn’t work when using browsers (Safari, Firefox, Chrome on Mac; Firefox, Chrome on Windows). Not sure what magic needs to happen to make shortnames work when typing them into the browsers’ address bar. Guessing some search function overrides local dns lookups.
Any ideas?
Thanks for the post and comments. Great stuff in here.
//Shawn
Hey Shawn,
Thanks for the kind comment and I’m sure we can get this working for you. My first guess is that your network interface doesn’t have an entry/entries for the domain suffix to use when a short name is provided. The suffix list lets the machine know what domains to append to any short name when attempting name resolution. If I run the command ipconfig and review the results for the relevant interface (I have a bunch of them) I can see that one of the entries is ‘Connection-specific DNS Suffix : localdomain’ – when I ping the short names my machine makes the assumption that I meant to add that suffix to the end. You can also check this using PowerShell –
PS C:\> (Get-DNSClient).Suffix
localdomain
As a test you could use PowerShell to set the suffix to your desired entry and then test again. You could also set this in the GUI for the adaptor if you are more familiar with that or have set a static IP.
With PowerShell the command would be similar to the below –
PS C:\> Set-DnsClient -ConnectionSpecificSuffix localdomain -InterfaceAlias Ethernet
Obviously you can swap the suffix and interface alias for the correct ones on your machine. You’ll likely need to run the shell as administrator for it to make the change. Additionally if you’re using pfSense as a DHCP server make sure the right suffix is listed and that way machines will receive it automatically. Let me know how you get on with that and if you need any other suggestions – hopefully this resolves it for you but if not comment back here.
Alex
Hi Alex,
I’ve spent DAYS trying to make this happen! Your post briefly gave me hope.
Example is my Unifi Cloud-Key with pfSense static DHCP reservation 10.39.10.209
Resolver has both Register boxes checked.
After reading your post:
DHCP now has explicit Gateway/Domain (even though these are the defaults)
Tried adding private.lan to domain search list
No change
chris@machine:~$ arp -a
unifi.private.lan (10.39.10.209) at 18:e8:ab:cd:ef:12 [ether] on enp0s25
_gateway (10.39.10.1) at 00:08:a1:23:45:67 [ether] on enp0s25
chris@machine:~$ ping unifi
ping: unifi: Name or service not known
chris@machine:~$ nslookup unifi
Server: 127.0.0.53
Address: 127.0.0.53#53
** server can’t find unifi: SERVFAIL
FQDN works just fine:
chris@machine:~$ nslookup unifi.private.lan
Server: 127.0.0.53
Address: 127.0.0.53#53
Non-authoritative answer:
Name: unifi.private.lan
Address: 10.39.10.209
Config is as simple as it can get: Ubuntu laptop, Cloud-Key, FlexHD AP plugged into LAN1, 2, 3 of SG3100 802.1q switch ports providing untagged Management_VLAN 10.39.10.0/24. WAN parasites off another firewall for this test rig (so double-NAT) but this shouldn’t affect anything in local name resolution. NAT rule forwards lan port 53 traffic to 127.0.0.1
What other magic dust have you got in your setup that makes it work — AD of course.
Can name (not FQDN) resolution work without AD?
Chris
Hi Alex
My question didn’t make it to your site (yet???).
In case it does make it later (after moderation or whatever), PROBLEM SOLVED.
Issue was that my Ubuntu laptop did not know it was in private.lan domain.
Moving laptop from manually typed fixed IP to reserved static IP in pfSense DHCP server fixed it.
Thanks for your nicely written article …and for forcing me to think.
Chris
Hi Chris,
A while back I changed comments on here to be approved only as even with the spam filtering, stuff was still getting through. I was going to ask whether you’ve configured the DNS suffix/dns-search option for the interface/box. Now that you’re getting an address from pfSense it is going to update that for you but if you were statically assigning you’d need to set it yourself.
I’m glad you got to the bottom of it, always nice to know the stuff I write has been helpful in some way.
Alex
You mentioned at the beginning you forward this to your DNS servers on Windows. Can you explain how you do that step?
Hi Ems,
Depending on your use case and needs, I’d start with the first link below and see if that’s appropriate.
https://docs.netgate.com/pfsense/en/latest/services/dns/resolver-domain-overrides.html#dns-domain-overrides
https://docs.netgate.com/pfsense/en/latest/services/dns/forwarder-overrides.html#domain-overrides
If you have firewall rules or complex routing, you’ll need to take those things into consideration to make sure traffic flows appropriately.
Hope this helps but feel free to provide more information or ask further questions.
Alex